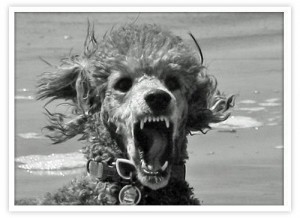
What is Poodle SSL 3.0 vulnerability and why we should care?
We highly recommend that use of SSL 3.0 be disabled on all websites.
The vulnerability allows an eavesdropper to review of presumed encrypted conversation between a client and server using SSL 3.0.
Handling of blocks of data are encrypted under a specific type of encryption algorithm within the SSL protocol is the cause for the vulnerability. The “Poodle” attack focuses on SSL/TLS negotiation to use the older method of SSL 3.0. The use SSL 3.0 allows for traffic to be decrypted by a third party seeing the conversation between client and server. This attack method typically causes a lot of client/server traffic because it is done byte by byte with many sessions opened between client and server.
Though TLS is not vulnerable to this method, it can be implemented by a client requesting a lower level of TLS, aka SSL 3.0. The attack will be mostly manifested by a Man in the Middle watching for packets on a public wifi that are using SSL 3.0.
To ensure your clientele are not affected by this bug, we recommend that SSL 3.0 be disabled.
REFERENCES
https://www.us-cert.gov/ncas/alerts/TA14-290A
http://www.kb.cert.org/vuls/id/577193
http://www.hostdime.com/blog/poodle-vulnerability/



Comments
No comment yet.